I cast an idle eye over the TV in my landlady’s living room. A handsome cop in a car enraptured her. The cop radioed his partner back at HQ to tell his wife he’d be back late that night.
‘That’s rude’, I mumbled, ‘… text her yourself’.
The camera shot widened and, from the shape of the car, I saw the era predated the mobile phone. My landlady snorted.
“OK then”, said I, leaving the rent money on an expectant table. Fingering the remote, she turned the volume up as I edged out the door.

Photo: Pinterest: Fargo Season 2
A good narrative depends on the suspension of disbelief. Authors want readers immersed in their story, caring about the characters as if they were real. Plot details that jar, niggle or provoke disbelieving wisecracks are simply no good.
Even in fantasy or science fiction, limits apply. The imaginary world conjured up by an author must cohere internally. Tolkien cannot suddenly have hobbits donning jet-packs to cross mountains. That technology does not plausibly exist in Middle Earth.
But what if technology does exist and is conspicuously not used by a character caught in a fix? A lacuna such as the cop not phoning his wife himself may interrupt the flow of a story. Indeed, returning to Tolkien, one may ask why the hobbits undertook such an arduous trek through hostile terrain to Mordor when well-disposed, giant flying eagles existed all along.

Photo from: http://www.blu-ray.com
For mystery and thriller writers, constant, wondrous advances in technology create potential plot pitfalls for stories set in the present day. Many of the logistical crises faced by characters just a few decades ago make no sense in a world of mobile phones. Authors who now wish to have a character incommunicado must explain that their phone went dead, lost coverage or was smashed. Fortunately, almost every writer covers this base.
A base less well covered is the false backstory. Many thrillers depend on a character successfully misrepresenting himself. A dashing fellow tells an heiress he is an unmarried romance novel writer. A seemingly well-heeled tycoon mentions his stint at Cambridge. An undercover cop infiltrating a syndicate presents himself as a hippie with ‘lots of mates’ in the Boston nightclub scene. Whatever the backstory provided, only the most gullible protagonist would not google a new associate upon whom they intend to bestow some trust. This includes checking whether their social media profile matches what they say about themselves and, if the stakes are high, scraping other data from the web.
One does not have to be particularly adept at googling to know that even the absence of a social media footprint blares like a vuvuzela. Consequently, a plausible cad, fraudster or agent needs to have generated fake Facebook accounts, twitter feeds and to somehow simulate the digital trail most people in the developed world inevitably leave behind as they move through life.
Let’s not forget about all the apps out there. Google Maps, for example, renders superfluous a turn in many books and movies that I find quite atmospheric. This is where a sleuth pulls up at to a vacant lot discovering that it is not an apartment building or row of fancy offices like the business card said. Street View would have saved anyone with 2MB of data the downtown trip.
A related scene is where the brave hero enters the villain’s lair, dodging guards ambling in the grounds. There, he tiptoes into the library, jimmies open a cabinet or desk, rifles through papers and stashes the incriminating folios in a pocket. A surprising number of novels still contain this antiquated event. With most information nowadays stored on computers, rifling is a virtual rather than a physical event. What’s more, a hacker competent enough to crack a password on site, could probably just as well do it remotely when the user is on-line. So, the hacker does not have to tiptoe into the library to get information. The narrative problem is that a geek tapping at a keyboard from a beanbag at a coffee-shop across town does not introduce nearly as much menace to a storyline as a gung-ho, former Navy Seal breaking and entering.
I recently read an account of an unpleasant bodyguard forcing a by-stander to delete from their phone photographs just taken. A few decades ago, the equivalent episode would have seen the surly goon contemptuously stripping the Kodak film from the camera exposing the negatives to the light. Except today destruction of data is a bit trickier. Free software allows anyone to ‘undelete’ lost images and an increasing number of digital natives know this. If your goon merely deletes data or crunches a camera underfoot, younger readers will lose all respect for his intellect, wondering, “why didn’t he take the memory card?” If this tiny, flat piece of circuitry survives, the photographs still exist.

Photo: Scene from Call Northside 777
In my day-job I often present evidence of misconduct gleaned from an employee’s own SIM card. The other day, a witness spent an hour on the stand trying to explain his after-hour trips to the home of a CEO tendering for a rather big contract. The employee was senior. He sat on the committee deciding who got the contract. Naughty…. While studiously avoiding incriminating phone-calls, the guy’s automatically saved Uber receipts gave the game away.
I wonder why crime bosses, real or fictional, do not similarly subject their underlings’ phones to quick, random forensic scrutiny. Why not have their own risk management department schedule probity checks for, shall we say, conflicts of interest? A Don need not bother with a subpoena or warrant. A gun waved in a face would ensure compliance most effectively.
I’ll end with the most rapidly developing field of science, biometrics. It presents plenty of potential plot problems. Not only for authors but actual handlers of secret agents too. Consider the need for a spy, real or imagined, to travel under an assumed identity to another country. Unlike five years ago, his passage is not secured any longer by a piece of paper. As Jeff Stein says in Wired magazine:
‘Busy spy crossroads such as Dubai, Jordan, India and many E.U. points of entry are employing iris scanners to link eyeballs irrevocably to a particular name.’
If James Bond has travelled within the EU before, even as a youngster, this means his eyes would give him away should he later pass himself off as someone else. His facial biometrics will give him away in Australia. False, cross-border identities may still be a plot device but not a very plausible one when an agent has ‘gone rogue’ or has travelled under a different name before. Stein again:
‘If you go to one of those countries under an alias, you can’t go again under another name,” explains a career spook, who spoke on condition of anonymity because he remains an agency consultant. “So it’s a one-time thing — one and done. The biometric data on your passport, and maybe your iris, too, has been linked forever to whatever name was on your passport the first time. You can’t show up again under a different name with the same data.”’
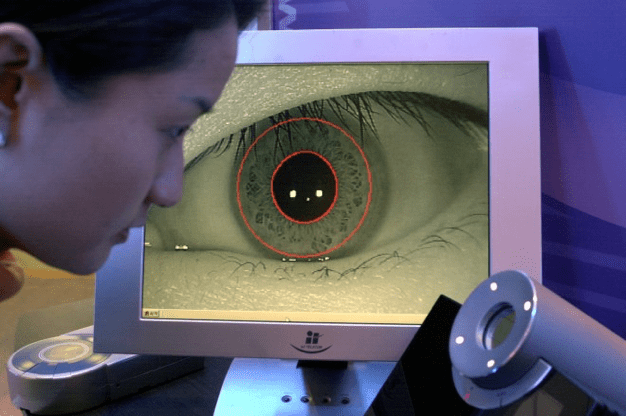
Photo from: Wired Magazine
Biometrics also means the useful trope of the backstreet passport forger is a thing of the past. A successful forger these days would need to have high level state connections in several countries. Even sneaking into building with a false ID badge rings false. As gruesome as it sounds, in the place of the forger, author’s now need to invent a surgeon adept at borrowing fingers or eyes for a character to gain access to buildings.
For younger readers who have grown up googling, undeleting, swapping SIM cards and pressing their fingers to scanners many of the crises facing our characters in mysteries or thrillers may seem lame. For authors, there is thus yet another task – keeping reasonably abreast of advances in digital technology. Or writing books, damn it all, set in an era before the advent of computers spoiled vacant lots, false identities, rifling through desks and being uncontactable on a lonely road.

Bio: Heinrich grew up in rural South Africa. His work takes him all over Africa. Heinrich prosecutes corruption cases in South Africa’s public service and trains investigative journalists. He is the author of Sarie.
First, allow me to congratulate you Heinrich on a wonderful and thought-provoking post.
Secondly, thanks for giving me the “heads-up” about it and inviting me to comment as a former undercover cop [author of Undercover: Operation Julie – The Inside Story]. My undercover days were pioneering in the UK and as part of what is still the UK’s biggest drug bust, my undercover partner and I made up the “rules” as we went along.
Please understand all my my observations below are “off the top of my head.” The whole subject is fascinating to me and worthy of an in-depth response. Alas! My writing commitments prevent such a thing 🙂
All this was back in the 1970’s. Nowadays undercover cops have a whole “back room staff” to facilitate many things such as establishing and cementing a “legend” – a false identity. It’s all part of their back story and no doubt far more sophisticated now than back in the day.
I was supplied with a drivers’ licence in a false name and a fake criminal record was set up in that new and fake identity. It was sufficient then to enable me to work deep undercover for a lengthy period.
In my view it would not be sufficient now. As you rightly point out, social media is huge now. I would almost certainly have insisted on a fake Facebook account at least. Of course, that brings its own potential problems. The more of a footprint you leave, the more likely it is you will be found out.
I operated in pre-mobile phone days. I expect most current undercover agents carry at least one mobile phone. That is a two-edged sword. On one hand, the agent can be located to within a short distance of a radio mast owing to modern technology thus offering a degree of protection for the agent. On the other hand, its innards can be “interrogated” and I’m sure sophisticated organised criminal gangs (OCG’s) have the capability to do just that – scary!
Biometrics is another matter. As Heinrich mentions, items such as passports were relatively easy to forge years ago – not now. Iris recognition is yet another layer designed to assist the “good guys” in the fight against crime. But as that technology increases, as it surely will, then OCG’s will step up their own game and utilize the same technology in order to check out the bona fides of a new face in their midst.
Fortunately, for my successors and for crime writers, I think there will always be the “lone wolf” operating clandestinely. He or she has little ID, uses cash and keeps a low profile. That agent will undoubtedly claim, as part of his/her back story, all this is a deliberate ploy to avoid detection by law enforcement.
The real skills involved in successful undercover work are akin to being an Oscar-winning performance as an actor.
Technology can hinder as well as assist such brave people.
Once more, I congratulate Heinrich on such a thoughtful article. Well done!
LikeLiked by 2 people
Hi Heinrich,
Great article. All four of my books so far have been written pre-cell phone and technology but I am about to set one in current SA. Facebook and Wats App are going to play a role so it will be interesting….
LikeLiked by 3 people
Thanks Sarah and Stephen for your kind words. I’m intrigued, Stephen, by the creation of a legend through Facebook, Twitter, etc for an undercover officer. What a difficult task. Unless these timelines and feeds were planned and kept alive long in advance, it seems to me that a half-serious Links Analysis would defeat the ruse. I mean there’d surely be little density to the posts and little cross-reference to other identifiable people or events. This is unless someone maintains a Truman Show-like compound of fake identities each bantering with each other. But I suppose a limited social media presence could, as you suggest, be explained away by a legend that the agent was for some reason very discrete. Thanks for sharing you experiences.
LikeLiked by 2 people
This is exactly why I’m setting my detective in a 1920s fictional town. I can’t imagine trying to navigate the labyrinth of technology to create a plausible plot. BTW: You’re so right about Tolkien’s eagles, LOL! Thanks 🙂
LikeLiked by 4 people
In my view it would not be sufficient now.
LikeLiked by 1 person